
By Joseph Bryson April 14, 2026
ACH payments can be efficient, affordable, and easier to manage than cards or paper checks. But that efficiency cuts both ways. If your team processes a fraudulent ACH authorization form, the damage can spread quickly through operations, cash flow, customer relationships, and compliance workflows.
A bad authorization can lead to unauthorized returns, disputed debits, payment reversals, internal rework, bank scrutiny, and avoidable losses. It can also create a recordkeeping problem: if a customer disputes the debit and your team cannot prove clear authorization, the payment may become difficult to defend.
For recurring billing, the risk compounds because one weak setup can trigger multiple failed or disputed debits over time. Regulation E requires written authorization for preauthorized transfers from a consumer account, signed or similarly authenticated, and requires the party obtaining the authorization to provide a copy to the consumer.
NACHA also emphasizes retaining proof of authorization and being able to produce it when requested.
That is why ACH fraud prevention starts well before funds move. The real control point is the review stage. Before finance, operations, or billing teams process an ACH debit, they need to know how to spot suspicious forms, verify account-holder intent, and pause questionable submissions before they turn into returns or fraud losses.
This guide explains how to identify a fake ACH authorization, what warning signs matter most, how to review paper, PDF, emailed, online, and e-sign submissions, and what internal controls reduce exposure.
The goal is practical ACH authorization fraud detection: not perfect certainty, but a repeatable process that helps you make better decisions before you process the payment.
What an ACH authorization form is and why it matters before you process a debit
An ACH authorization form is the record that shows a customer or account holder gave permission for a business to debit or credit a bank account through the ACH network.
In practical terms, it is the document or electronic record that connects customer consent to the actual payment instruction. If that authorization is weak, unclear, altered, incomplete, or unauthorized, the payment is exposed before it even enters your system.
A good form does more than capture bank details. It should clearly state who is authorizing the payment, whether the debit is one-time or recurring, how much will be charged or how the amount will be determined, when the debit will occur, and how the customer can revoke or cancel authorization.
If those elements are unclear, even a form that looks legitimate can create disputes later. That is one reason businesses often review what an ACH authorization form is and how authorization language should be structured before building their internal workflow.
The importance of the form changes depending on your business model. A one-time invoice payment carries one type of risk. A recurring billing setup for memberships, retainers, service contracts, tuition, rent, or installment plans carries another.
Recurring debits can generate more disputes because customers may later challenge the timing, amount, cancellation status, or whether they approved recurring withdrawals in the first place.
For consumer preauthorized debits, the form also matters because the authorization must be in writing and signed or similarly authenticated, and the customer must receive a copy.
For internet-initiated entries, NACHA has also published guidance stressing the importance of keeping evidence that authorization actually occurred and retaining that record for a defined period after termination or revocation.
The operational lesson is simple: do not treat the form as paperwork. Treat it as a risk-control document. If your team sees ACH authorization verification as a required control step rather than an administrative task, your chances of catching suspicious ACH payment forms before processing go up significantly.
Why authorization quality matters as much as authorization existence
Many teams focus only on whether a form exists. That is not enough. A form can exist and still be defective, misleading, or fraudulent. A copied signature pasted onto a PDF, a routing number paired with someone else’s account name, or vague recurring terms can all create real risk even though the document appears complete at first glance.
Authorization quality matters because disputes often turn on specifics. Did the account holder actually agree? Did the form clearly describe the amount and frequency? Can the business show when and how the approval happened? Can it connect the person who submitted the form to the account holder with reasonable confidence? These questions matter in ACH fraud detection methods and in downstream dispute handling.
For example, a form that says “I authorize monthly payments as needed” sounds convenient, but it creates uncertainty. What amount? On what day? Under what service agreement? If the customer later says the amount was not what they expected, your proof may not be strong enough. A vague form is not necessarily fake, but it is still risky.
Why fraudulent forms are so damaging in real operations
A fraudulent or defective ACH authorization rarely causes just one problem. It tends to trigger a chain reaction. The payment may be returned. The billing team may have to contact the customer.
Collections may be delayed. Service may be interrupted. The processor may ask for supporting documentation. Management may want to know why the form was accepted in the first place.
Unauthorized returns matter because they are not just operational setbacks. They can become risk indicators. NACHA has long distinguished unauthorized return reasons such as R10, R07, and R29, and businesses that accumulate too many authorization-related problems may face more scrutiny from processing partners or banks.
Businesses that understand ACH return codes are usually better equipped to connect poor front-end review with downstream payment issues.
There is also a reputational dimension. If a legitimate customer believes your business debited an account without proper approval, trust drops quickly. Even when the issue came from a fake form submitted by a bad actor, the customer often experiences it as your company’s failure to verify the request.
That is why ACH payment fraud prevention should start with a disciplined intake and review process rather than relying on return handling after the fact.
Common ACH fraud scenarios businesses run into

Fraud involving ACH authorization is not limited to obvious forgeries. In many cases, the fraud is subtle, mixed with real customer information, or hidden inside ordinary workflows like remote onboarding or email-based payment collection. Understanding the most common patterns makes it easier to identify a fraudulent ACH authorization form before processing.
One frequent scenario is the altered form. A legitimate-looking PDF is submitted with a real customer name and address, but the bank account information was changed. The form may have been copied from an earlier agreement, edited, and resent. If your staff checks only the signature block and amount, the mismatch may go unnoticed.
Another common scenario is unauthorized submission by someone inside the customer’s organization. In B2B invoicing, a staff member may send banking details and approve ACH setup without actual authority to bind the business or authorize debits from that account. The submission may not look fake at all, but it is still unauthorized if the signer lacks authority.
A third scenario involves remote onboarding. A first-time customer completes a web form, uploads a signed authorization, and asks for immediate service activation.
The contact email uses a generic domain, the phone number does not match public business records, and the bank information cannot be linked to the legal entity on file. This is a classic case where convenience-driven onboarding can overwhelm proper ACH risk review process controls.
Email compromise is another major risk. A known customer’s inbox may be compromised, and your team receives what appears to be a routine ACH setup or bank-change request. Because the email comes from the right address, the message feels trustworthy.
But the attached authorization form contains new bank details controlled by a fraudster. Recent industry guidance on ACH fraud trends continues to emphasize scams disguised as legitimate payment instructions, including business email compromise scenarios.
Then there is the incomplete authorization scenario. The customer may have intended to pay, but the form is missing key terms, unclear on recurring frequency, or lacks a valid signature trail. That may not be criminal fraud, but it still creates processing risk and can lead to unauthorized returns or disputes later.
The takeaway is important: not every bad form is obviously fake, and not every risky form is intentionally fraudulent. Your review process needs to catch both.
Fake, altered, and copied forms
Fake ACH authorization forms are often built to look ordinary. Fraudsters know that finance teams expect standard layouts, signature boxes, and routing/account fields. So they imitate normal documents, sometimes using a real company logo or copying a previous form the business already recognizes.
Altered forms are especially dangerous because they contain enough real information to lower suspicion. A valid service agreement may exist. The payer name may be correct. The address may match.
But the account details, effective date, or recurring frequency may have been changed. If your process does not include document consistency review, your team may not notice that the form was modified after the original approval.
Copied banking details also create risk. A fraudster may reuse account and routing information stolen from another source and pair it with a different payer identity. In that case, the authorization form may not fail basic formatting checks, but it still does not represent a legitimate authorization from the account holder.
This is why verifying ACH authorization forms should involve more than confirming that all fields are filled. You need to ask whether the pieces fit together.
Unauthorized but not obviously fake submissions
Some of the hardest cases involve submissions that are not forged in the traditional sense. The form may be signed by a real person, sent from a real email address, and attached to a real business relationship. Yet it is still unauthorized because the signer did not have authority or the approval did not match the actual debit setup.
This happens in business settings when an employee signs an ACH form even though only an owner, controller, or designated finance officer can authorize payment instructions. It also happens when a customer agrees to a one-time payment but the form is set up as recurring, or when a verbal approval is treated as broad written consent.
These situations often lead to arguments later: “I approved the first payment, not ongoing debits,” or “That employee was not allowed to sign.” Your process should be built to catch these issues before the first debit is sent.
The clearest warning signs of a fraudulent ACH authorization form
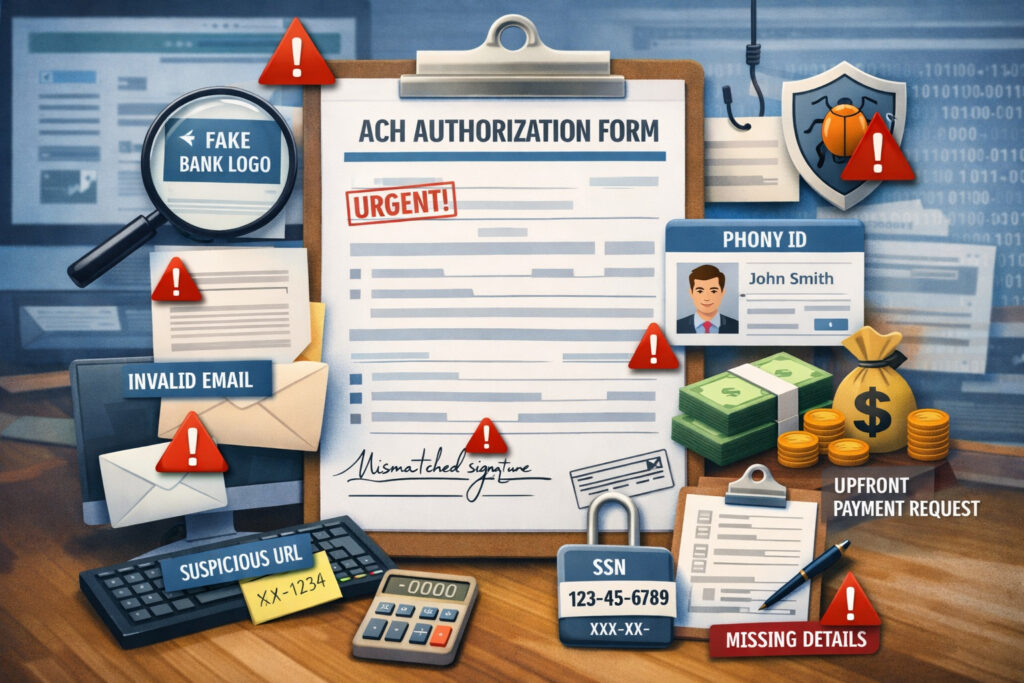
Most suspicious ACH payment forms reveal themselves through patterns, not a single clue. A mismatch in one field may be a typo. Two or three inconsistencies together should move the form into a higher-risk category. Strong ACH authorization fraud detection depends on teaching reviewers to spot clusters of red flags.
Start with mismatched customer information. If the account holder name does not align with the payer name, billing contact, business name, or service agreement, stop and investigate.
The same applies when the routing number corresponds to a financial institution that seems inconsistent with the customer profile, or when the address on the form conflicts with the address you have on file.
Signatures deserve careful attention too. A signature image alone is weak evidence if the rest of the submission lacks context. Look for signatures that appear pasted, unusually crisp compared with the rest of the scan, inconsistent across pages, or detached from the actual account holder identity.
With electronic workflows, look beyond the visual signature and review timestamps, email verification, IP logs, device data, and event history.
Formatting issues matter more than many teams realize. Fraudulent forms often show uneven fonts, inconsistent spacing, mismatched branding, blurred edits, partial page cropping, missing headers, or text boxes placed over original content.
These are classic signs of post-creation editing. The same is true when a PDF metadata trail or e-sign audit trail is absent where one would normally exist.
Behavioral clues are equally important. Fraudsters often push for speed. They may submit forms late in the day, ask for same-day processing, resist callback verification, or avoid live conversation.
Disposable email addresses, phone numbers that go to voicemail only, and reluctance to provide supporting information are all relevant payment authorization fraud red flags.
The form language itself can be a risk marker. If the authorization statement is vague, fails to specify recurring frequency, omits revocation instructions, or does not clearly describe the amount or billing method, the form may be defective even if it is not forged.
For consumer recurring debits, that weakness matters because the authorization must be clear enough to support the debit and comply with applicable rules.
Below is a practical review table your team can use when screening a fraudulent ACH authorization form before processing.
| Red flag | Why it matters | Recommended action |
| Account holder name does not match customer or contract | Suggests unauthorized use of account or data entry manipulation | Pause processing and verify ownership directly |
| Signature appears pasted or inconsistent | May indicate altered or copied authorization | Request fresh authorization through secure workflow |
| Form has uneven fonts, edits, or cropped sections | Common sign of PDF tampering or manual alteration | Reject document version and require resubmission |
| Recurring terms are vague or missing | Creates dispute risk even without obvious fraud | Return for clarification before setup |
| Email sender resists callback verification | Suggests impersonation or urgency fraud | Escalate for manual review |
| First-time customer requests immediate ACH debit with minimal history | Higher fraud exposure and less baseline data | Apply enhanced verification steps |
| Bank details changed after original agreement | Possible account redirection fraud | Confirm change using known contact information |
| Contact uses disposable or unrelated email domain | Weak identity confidence | Require additional identity validation |
| Business signer cannot show authority to bind account | May invalidate the authorization | Verify signer authority before processing |
| E-sign record lacks timestamp, IP, or completion trail | Weak evidence for later disputes | Treat as incomplete until audit record is available |
Mismatched account details and inconsistent customer information
One of the fastest ways to identify fake ACH authorization submissions is to compare the form against information already known about the customer. Fraud succeeds when teams treat the form as standalone. Fraud is often caught when teams compare it to the broader customer record.
Does the payer name match the legal name on the service agreement? Does the bank account appear to belong to the same business entity? Does the billing address match your CRM, invoice record, or onboarding packet? Does the signer’s email domain line up with the company they claim to represent? If the answer to several of these is no, the form should not be processed.
This matters in both B2B and consumer settings. In business payments, a mismatch may reveal that a staff member is using a personal account, a third-party account, or an account unrelated to the purchasing entity. In consumer settings, a mismatch may indicate stolen bank information or identity misuse.
The key is not to assume that a plausible explanation exists. There may be one, but your process should require that it be confirmed before the debit is originated.
Suspicious signatures, altered documents, and rushed submission behavior
Reviewers often overvalue a visible signature and undervalue how the document got to them. A signature is only one element of an authorization. Without a trustworthy capture process, it may offer little real protection.
Watch for image-based signatures pasted into PDFs, signatures that are identical across unrelated forms, or scanned pages where only one field appears digitally sharp while the rest looks handwritten or low-resolution. These clues do not prove fraud on their own, but they strongly support additional review.
Rushed behavior is another major indicator. Fraudsters prefer pressure because pressure shortens verification. They may say the customer is traveling, the invoice must be settled today, service will be lost if payment is not taken immediately, or management already approved the request. None of that should bypass your controls.
How to identify fake ACH authorization submissions by channel
Different submission channels create different risks. A paper form handed over in person raises one set of review questions. An emailed PDF, online form, or e-sign workflow raises another. Businesses that want stronger ACH fraud detection methods should review forms based on both content and channel.
Paper forms may feel safer because they are tangible, but they are not automatically more reliable. They can be copied, altered, or completed by someone without authority. The advantage of paper is that you may be able to compare handwriting, verify identity in person, or collect supporting documentation at the same time.
PDF and email submissions are higher risk because they are easy to edit and easy to impersonate. Fraudsters can reuse templates, paste in signatures, or send altered forms from compromised or lookalike email accounts. If your team accepts emailed ACH forms, document consistency review becomes critical.
Online web forms can be strong if they include proper controls such as authenticated login, session tracking, IP logging, confirmation screens, and secure delivery of the final authorization copy.
They can also be weak if they rely only on a checkbox and bank fields without meaningful identity verification. For WEB entries, NACHA has published industry practices stressing that businesses should maintain adequate records evidencing authorization.
E-sign workflows can offer some of the best evidence, but only if they are configured well. A typed name in a box is not enough by itself. Stronger workflows capture timestamps, signer email verification, IP or device context, version history, and proof of the exact text presented at signing. Weak e-sign setups may look polished while producing little usable evidence later.
The rule for all channels is the same: process confidence should be based on evidence, not convenience.
Paper forms and scanned documents
Paper authorizations still appear in many industries, especially in field services, home services, property management, healthcare-adjacent billing, tuition collection, and business account onboarding. They can work well when collected in person, but they can also become risky once scanned, emailed, or re-entered manually.
When reviewing a paper or scanned form, inspect whether the handwriting looks consistent across the document, whether all pages appear to come from the same original file, and whether the bank details appear to have been inserted in a different pen, typeface, or image layer.
If the form is a scan, zoom in on the signature area and bank fields. Signs of cut-and-paste editing often become more obvious at close range.
It is also worth checking whether the form version matches your current approved template. Fraudsters sometimes use old forms found in prior email chains or public-facing materials. An outdated form is not always fraudulent, but if it lacks newer controls or required fields, your team should replace it with the current version before processing.
Emailed PDFs and attachments
Emailed ACH authorizations are convenient, but they are one of the easiest channels to abuse. The document may be altered, and the email itself may be spoofed, compromised, or sent by someone who is not authorized to submit bank instructions.
Review the sender address carefully. Look for subtle misspellings, unusual reply-to addresses, sudden shifts from the customer’s normal communication style, and unexpected changes in payment behavior. If a long-time customer who usually pays by check suddenly emails a PDF requesting recurring ACH debits from a new account, that should trigger enhanced review.
Do not rely on email thread history alone. A compromised mailbox can preserve the appearance of continuity. For higher-risk requests, use a known phone number already on file, not the one listed in the suspicious email, and confirm the authorization with the account holder or authorized contact.
This is especially important for change requests. New authorizations are risky, but change-of-bank instructions inside existing relationships are often where fraud causes the largest losses.
Online forms and e-sign workflows
Online ACH forms and e-sign tools can make ACH authorization verification more reliable when they are designed well. They can also create false confidence when teams assume “electronic” means “verified.”
A strong online workflow should tie the authorization to an authenticated session or a verified customer channel. It should record the date and time of submission, preserve the exact language shown at the time of consent, and generate an audit trail that can later demonstrate identity and assent. For recurring billing, it should also state the schedule clearly and provide a copy of the completed authorization.
A weak workflow typically has one or more of these issues: no meaningful authentication, no completion log, no clear record of the form version, no proof the final authorization was delivered, or no verification that the signer is the account holder or authorized representative.
If your current online process would make it difficult to answer “Who approved this, when, using what workflow, and what exactly did they see?” then your risk is higher than it looks.
When incomplete or vague authorization language creates risk

Not every problematic ACH form is fraudulent in the traditional sense. Some forms create risk because they are vague, incomplete, or poorly written. This is a different problem, but it can lead to many of the same outcomes: disputes, unauthorized returns, payment delays, and trouble proving customer consent.
An authorization should identify the type of payment clearly. Is it one-time or recurring? If recurring, what is the frequency? If the amount varies, how is it calculated? What notice will be provided if the amount changes? What is the effective date? How can the payer revoke authorization? If those answers are buried, missing, or overly broad, the business may have trouble defending the debit later.
This issue becomes especially important when teams reuse generic templates. A broad form designed for multiple billing models may not fit the specific transaction at hand. For example, a service agreement may mention payment by ACH, but that alone may not be enough to support a separate recurring debit setup if the frequency and amount are not spelled out clearly.
Resources on setting up an ACH authorization form often emphasize that the strongest authorizations are specific, retrievable, and connected to the actual billing workflow. That practical point matters as much as any legal language.
Vague authorizations also create internal confusion. When operations staff are not sure what the customer approved, they improvise. Improvisation leads to preventable mistakes.
Examples of risky authorization language
Here are a few examples of language that should prompt review:
- “I authorize payments as needed.”
- “Charge my account monthly.”
- “Debit any outstanding balance.”
- “Use ACH for future invoices.”
- “I agree to pay electronically.”
These statements sound convenient, but they leave out too much. They may not specify whether the authorization is one-time or recurring, how amounts are determined, what the timing is, or how the customer can stop future debits.
By contrast, stronger language usually identifies the business, states the debit type, describes the amount or method for determining the amount, includes the timing or frequency, and explains revocation or cancellation.
Why weak language leads to fraud exposure
Weak language does not just create compliance ambiguity. It can also make fraud easier. A bad actor can hide inside unclear terms.
If the form says “future invoices” without defining limits, frequency, or notification, a fraudster who gained access to the customer’s email or account may be able to submit or alter billing instructions in a way that looks arguable rather than obviously fake.
That is why good ACH debit fraud prevention includes improving the authorization itself. Better language narrows the room for impersonation, misunderstanding, and internal error. It also gives reviewers clearer criteria for approval.
Practical ACH fraud detection methods before processing
Good ACH fraud detection methods are layered. No single control catches every bad form. The strongest approach combines identity checks, account validation, document review, approval workflows, and targeted escalation for higher-risk cases.
Start with identity verification. Make sure the person submitting the authorization is who they claim to be. For a consumer, that may mean matching the contact information, confirming ownership of the email or phone number, and reviewing whether the name aligns with the bank account and service relationship.
For a business payer, it may mean confirming that the signer is an authorized representative with authority to approve ACH debits.
Next, validate account ownership where appropriate. NACHA’s account validation resources highlight the importance of validating first-use consumer account information for certain ACH payments.
Even when a specific rule does not apply to your exact workflow, account validation is still a smart fraud control because it reduces the chance that the bank details belong to someone else.
Then review the document itself. Look for consistency between the form, the service agreement, customer communications, and the account history.
Does the form version look legitimate? Are the dates logical? Is the recurring schedule aligned with the contract? Does the bank account change make business sense? If not, ask more questions before you process.
For higher-risk cases, callback verification remains one of the most practical controls. Call the customer using a known number already on file, not the phone number on the submitted form, and confirm that the authorization is genuine. This is especially useful for first-time large debits, remote onboarding, or any change in bank instructions.
Internal approval workflows also matter. A single reviewer under time pressure is more likely to miss red flags. A dual-review or approval threshold process is one of the simplest ways to strengthen ACH payment fraud prevention.
Identity verification and signer authority checks
Identity verification is often discussed, but not always implemented consistently. For consumer accounts, basic identity confidence may come from matching the submitted name, billing address, customer record, email, phone, and payment history. For business accounts, the review should go further and confirm signer authority.
Ask practical questions:
- Is this person already listed as an authorized contact?
- Does their job title support payment authority?
- Does the email domain match the business?
- Has your team worked with them before?
- Is the request consistent with how this customer normally pays?
If the answer to several of these questions is uncertain, you may need additional evidence, such as a callback to a controller, owner, or existing AP contact.
This step is especially important in B2B invoicing because unauthorized internal submissions are easy to miss. A real employee can still submit an invalid authorization.
Account ownership validation and recurring setup confirmation
Account ownership validation is one of the most practical forms of ACH authorization verification because it tests whether the bank details are plausibly linked to the account holder. This can be done through your processor’s tools, through commercially available bank-account validation solutions, or through risk-based internal steps depending on your setup.
For recurring payment setups, confirmation is equally important. A one-time debit authorization should not silently become recurring just because the customer used a bank form once. Send a confirmation that clearly states the recurring amount or billing method, schedule, and start date. Require the customer to review those details before the recurring plan goes live.
This is not just a good customer experience. It is also a strong fraud control because it creates another checkpoint where unauthorized or altered setup details can be caught.
Document consistency review and approval workflows
Document consistency review means comparing the ACH form to the rest of the file, not just reading it in isolation. The address, legal entity name, invoice record, signed contract, onboarding packet, and customer communications should tell a consistent story. If they do not, the reviewer should stop and resolve the discrepancy.
Approval workflows help enforce that discipline. For example:
- Low-risk recurring renewals from established customers may require one trained reviewer.
- First-time ACH debits above a threshold may require manager approval.
- Bank-change requests may require callback verification plus secondary approval.
- Remote onboarding with same-day processing requests may require fraud or compliance review.
That is what a functioning ACH risk review process looks like in practice: not a one-size-fits-all rule, but a risk-based workflow with clear escalation points.
When to pause, escalate, reject, or request more verification
One of the biggest mistakes businesses make is treating review as a choice between “process” and “decline.” In reality, most suspicious forms fall into one of four categories: safe to process, safe to process after added verification, not safe to process yet, or not acceptable at all.
Pause a form when something is off but potentially explainable. Maybe the signer title is unclear. Maybe the business recently changed banks. Maybe the form version is outdated but the customer relationship is real. In these cases, a pause protects the payment while giving the customer a chance to validate the details.
Escalate when the form shows multiple red flags, involves a large amount, concerns a first-time customer, or could expose the business to recurring debit disputes. Escalation should move the file to someone with authority and training to decide whether enhanced verification or rejection is appropriate.
Reject a form when the authorization appears altered, the signer cannot be verified, the bank information is inconsistent with the customer, or the customer refuses reasonable verification steps. Refusing to verify is itself meaningful information.
Request additional verification when the issue is incomplete rather than deceptive. For example, missing recurring terms, no proof of signer authority, or lack of a usable audit trail in an e-sign workflow may justify returning the form for correction rather than rejecting the relationship entirely.
This is where policy matters. Teams need clear standards so they are not improvising under pressure.
A practical escalation matrix
Use a structured approach like this:
- Process: Existing customer, no red flags, clear audit trail, matched information, standard amount.
- Process after added verification: Minor mismatch, first recurring setup, or small inconsistency that can be confirmed through known contact details.
- Pause and escalate: Multiple inconsistencies, urgent same-day request, bank-change request, first-time high-value debit, unverifiable signer.
- Reject: Altered document, refusal to verify, obvious impersonation, or bank details that cannot be tied to the customer.
This kind of matrix makes decision-making more consistent across shifts, teams, and offices.
What not to do when a form looks suspicious
Do not process “just this once.” Do not rely only on a signature image. Do not accept a new explanation by email without independent confirmation. Do not assume that because the amount is small, the risk is low. Fraudsters often test controls with smaller transactions before attempting larger ones.
And do not let front-line staff absorb the risk alone. If you want better ACH payment fraud prevention, staff must know they are expected to pause questionable submissions, not rewarded for pushing them through.
Real-world examples of suspicious ACH forms in common business workflows
Fraud screening becomes easier when you picture how bad forms appear in real operations. Here are common scenarios businesses run into.
A B2B customer with a history of paying by check emails a PDF requesting immediate ACH setup for future invoices. The sender is the office manager, but your contract lists the CFO as the billing authority.
The PDF looks clean, yet the bank account belongs to a different legal entity name than the one on the signed agreement. That form should not be processed without callback verification and signer authority review.
A recurring billing customer signs up online for a monthly service plan. The web form captures the bank account and a checkbox, but there is no reliable audit trail showing the full authorization text, no confirmed delivery of the final authorization, and no clear record that the customer agreed to recurring debits rather than a one-time payment. Even if the customer is real, the setup is weak and could become a dispute later.
A field-service technician sends in a paper authorization collected at the job site. The customer name matches, but the handwriting in the account fields is different from the rest of the form and the signature block appears unusually dark and sharp compared with the scanned page. That is a classic document consistency issue and should be reviewed before processing.
A remote onboarding prospect asks for same-day activation and submits a signed ACH form from a free email account. The phone number goes straight to voicemail.
The website for the business is newly created and the signer cannot be matched to public business records. That is not necessarily fraud, but it is a high-risk first-time customer and should be escalated.
These examples show why channel, context, and behavior matter alongside document review.
Example: service agreement plus altered ACH addendum
Suppose your company signs a service agreement with a business customer. A week later, someone emails an ACH authorization addendum with bank details for recurring billing. The pricing matches the contract, which lowers suspicion.
But the signer is a new contact not seen during sales or onboarding, and the signature on the addendum does not resemble the signature on the master agreement.
This is where teams often get caught. Because the core deal is real, the addendum gets less scrutiny. But the bank account instructions are a separate risk event. The right move is to verify the addendum directly with the authorized contact from the original agreement using known contact details. If the signer cannot be confirmed, the addendum should not be processed.
Example: first-time customer with an urgent remote submission
A new customer requests a large first payment by ACH to secure expedited service. The authorization is submitted by PDF, the email domain is generic, the business address is a virtual office, and the signer wants immediate confirmation that the payment has been “accepted.” This is a textbook environment for fraud pressure.
The business may still be legitimate. But the payment should not move forward until the customer passes enhanced identity review, account ownership validation, and callback verification. Fraud often depends on the receiving business treating urgency as proof of legitimacy. It is not.
Common mistakes businesses make during ACH authorization review
Many ACH losses do not happen because the red flags were invisible. They happen because the business ignored or minimized them. In practice, poor process discipline is often as dangerous as fraud itself.
One common mistake is processing forms too quickly. Teams under pressure to activate service, post payments, or close the month may treat ACH setup as clerical rather than risk-sensitive. That mindset leads reviewers to check whether the form is filled out, not whether it is trustworthy.
Another mistake is accepting altered forms without challenge. Staff may notice that the PDF looks edited, but still process it because the customer is known, the amount is expected, or the request seems routine. That is how altered bank details slip through.
A third mistake is relying only on a signature image. A signature without reliable context proves very little. Fraudsters know that visual signatures create false confidence.
Businesses also make errors by skipping customer verification for urgent requests, especially when the customer relationship appears valuable. Urgency is a risk factor, not a reason to lower controls.
Finally, many teams fail to document approval decisions. They verify something by phone, but do not record who was contacted, when, what was confirmed, or why the form was approved. Later, if the debit is challenged, the business has no usable internal record of its review.
These errors are preventable. The fix is not perfection. It is standardization.
Why “known customer” is not a sufficient control
A surprising number of fraud issues occur inside known relationships. A known customer can still experience email compromise. A known vendor can still have an unauthorized employee submit a form. A known account can still have its payment instructions changed by a fraudster.
That is why “we know them” should not replace process. It can affect the level of review, but it should not eliminate review entirely.
A better standard is: known customer plus matched account data plus expected payment behavior plus clean authorization trail. That combination is useful. Familiarity alone is not.
Why undocumented approvals cause downstream problems
When staff make a good decision but fail to document it, the business may still lose the benefit of that work. If the processor asks for proof, or if leadership later reviews the incident, undocumented review looks like no review.
Documentation should capture:
- who reviewed the form,
- what red flags were noted,
- what verification steps were completed,
- who approved the exception if one was granted,
- and where the supporting records are stored.
This is part of strong ACH risk mitigation and should be built into the workflow rather than left to memory.
Step-by-step checklist for reviewing an ACH authorization before processing
A review checklist helps turn judgment into a repeatable control. The best checklists are short enough to use every time but detailed enough to catch meaningful issues.
ACH authorization review checklist
- Confirm the payer identity
- Does the name on the form match the customer record, invoice, contract, or service agreement?
- If it is a business payer, does the legal entity name align?
- Confirm signer authority
- Is the person submitting or signing the form authorized to approve ACH debits for the account?
- If unclear, verify with an existing authorized contact.
- Check account detail consistency
- Do the routing number, account type, and account-holder details appear consistent with the customer?
- Does anything suggest a third-party or unrelated account?
- Review authorization language
- Is the form clearly one-time or recurring?
- Are amount, timing, and revocation terms understandable?
- Inspect the document for alteration
- Look for mismatched fonts, pasted signatures, cropped pages, overwritten fields, or inconsistent formatting.
- Review submission channel risk
- Was it submitted by paper, email, web form, or e-sign?
- Does the channel provide a reliable audit trail?
- Check for behavioral red flags
- Is the request unusually urgent?
- Is the customer resisting verification?
- Is this inconsistent with prior payment behavior?
- Validate account ownership where appropriate
- Use processor tools or internal validation steps for first-use or higher-risk scenarios.
- Confirm recurring setup details
- If recurring, has the customer received or acknowledged the exact recurring terms?
- Document the review outcome
- Record who reviewed the form, what was checked, any escalations, and the final decision.
How to use the checklist without slowing down the business
A checklist works best when paired with risk tiers. Not every form needs the same level of review. Established customers with low-risk recurring renewals may move quickly through the process. First-time high-value debits, bank-account changes, and remote urgent requests should trigger enhanced review.
The goal is not to create delay for every payment. The goal is to make sure the riskiest forms do not get processed with the same light touch as routine low-risk renewals.
How staff training, dual review, and standardized forms reduce fraud exposure
Technology helps, but people still make the go/no-go decision in many ACH workflows. That means staff training is not optional. A well-designed form will not protect you if employees do not know what suspicious ACH payment forms look like or when to escalate them.
Training should focus on realistic examples, not generic reminders. Show teams what altered PDFs look like. Explain why generic email domains matter. Teach the difference between a missing field, a weak authorization, and a high-risk fraud signal. Review recent return issues or internal incidents so staff can connect policy to real consequences.
Dual review is one of the most effective low-tech controls. A second trained reviewer catches issues the first person may miss, especially when the first reviewer is handling intake, customer communication, and time-sensitive processing all at once. Dual review is particularly valuable for first-time customers, bank changes, recurring debit setups, and larger dollar amounts.
Standardized forms reduce fraud by narrowing the range of what “normal” looks like. When your company uses consistent templates, approval fields, version controls, and capture methods, unusual forms become easier to spot. Standardization also reduces accidental defects such as missing revocation language or unclear recurring terms.
Documentation procedures matter too. If review steps, callback notes, and approval decisions are stored consistently, the business can defend its process later and improve it over time.
What effective ACH fraud training should include
Training should cover:
- the purpose of authorization review,
- common fraud scenarios,
- visual signs of altered forms,
- how to verify signer authority,
- when to use callback verification,
- how to document review decisions,
- and when not to process immediately.
It should also include channel-specific training. The red flags in a paper form are not identical to those in an e-sign workflow or emailed PDF.
A short annual training is rarely enough. The better approach is targeted refreshers tied to actual workflow changes, fraud incidents, processor feedback, or return trends.
Why standardized forms and version control matter
Businesses often underestimate the value of form discipline. If different departments use different ACH forms, reviewers lose the baseline needed to spot unusual documents. Fraud hides more easily when there is no consistent template.
Use one approved form set or one approved digital workflow for each payment type. Track version updates. Retire outdated forms. Require that special cases be routed through an exception process rather than creating ad hoc templates.
That structure makes verifying ACH authorization forms faster, not slower, because reviewers know what approved documents should look like.
Recordkeeping, audit trails, and processor requirements after the form is approved
A suspicious form review should not end once the debit is approved. Recordkeeping and audit trails are part of fraud control because they help your business respond to disputes, unauthorized return claims, and processor requests.
NACHA has published industry guidance emphasizing retention of authorization records and the ability to provide them when requested. Industry materials commonly reflect a two-year retention period tied to termination or revocation for relevant records, and businesses should align their storage practices with their processor, bank, and transaction type requirements.
That means storing more than just the signed form. Keep the final authorization text, e-sign audit logs, email confirmations, callback notes, version history, proof that the payer received a copy when required, and any later modifications or revocations. If a recurring authorization changes bank accounts or billing frequency, preserve both the old and new records.
Processor requirements matter here too. Some processors or banks expect quick production of proof when a debit is challenged. If your records are incomplete or hard to retrieve, the practical value of having a signed form drops sharply.
Good audit trails also support internal learning. If a return or dispute occurs, your team should be able to reconstruct what happened and identify whether the failure came from intake, review, approval, communication, or storage.
What records should be stored with each authorization
For each ACH authorization, consider storing:
- the final signed or electronically completed authorization,
- the exact form version used,
- timestamps and audit logs,
- the submission channel,
- the reviewer name and decision date,
- callback or verification notes,
- related contract or invoice reference,
- confirmation sent to the payer,
- and any subsequent change, revocation, or cancellation record.
This creates a defensible file rather than a loose collection of attachments.
Why recordkeeping reduces unauthorized return risk
When a customer disputes a debit, the speed and clarity of your response matter. A well-organized record can show the approval trail, the recurring terms, and the review steps taken before processing. A disorganized file makes even a legitimate debit harder to defend.
Businesses that already monitor ACH return codes often find that stronger proof-of-authorization files reduce the time spent investigating returns and help surface patterns that suggest front-end process weaknesses.
FAQs
How can I tell whether an ACH authorization form is fake or just incomplete?
A fake ACH authorization form often shows signs of impersonation, document alteration, mismatched customer information, or an account-holder identity that cannot be verified. An incomplete form may involve a real customer but still miss important details such as payment amount, recurring frequency, or cancellation terms. In either case, the safest step is to pause processing until the form is verified or corrected.
Is a signature enough to verify an ACH authorization?
No. A signature alone is not enough to confirm that an ACH authorization is valid. Businesses should also review account-holder identity, signer authority, submission method, account consistency, and supporting audit trail details such as timestamps or e-sign records. A signature image without context can be copied or reused and should never be treated as the only proof of authorization.
Should I process a suspicious ACH form if the customer says it is urgent?
No. Urgency is one of the most common fraud warning signs. If an ACH authorization form looks suspicious, the request should be paused for additional verification before any debit is processed. Fast turnaround requests, especially from first-time or remote customers, should increase the level of review rather than reduce it.
What is the safest way to verify a questionable ACH authorization?
The safest approach is independent verification. Contact the customer or authorized account representative using a phone number or contact method already on file, not the one listed on the submitted form or email. This helps confirm whether the payment instruction, bank account, and authorization details are legitimate before processing the ACH debit.
Are emailed ACH authorization forms always risky?
Not always, but emailed ACH forms are higher risk than many businesses assume. PDF attachments can be edited, email accounts can be compromised, and sender identities can be spoofed. For that reason, emailed forms should usually receive stronger document review and, when risk factors are present, callback verification before being approved.
What if the form looks real but the authorization wording is vague?
A form that looks professional can still create risk if the authorization language is unclear. If the wording does not clearly explain whether the payment is one-time or recurring, how much will be charged, when the debit will occur, or how authorization can be revoked, the form should be clarified before processing. Weak authorization wording can lead to disputes even when fraud is not obvious.
Do recurring ACH setups need extra review?
Yes. Recurring ACH payments usually require more careful review because they involve ongoing debits, future billing dates, cancellation rights, and stronger recordkeeping needs. Businesses should confirm that recurring terms are clearly stated, the customer knowingly approved them, and the final authorization record is stored in a way that supports future dispute handling if needed.
How long should ACH authorization records be kept?
Record retention practices can vary based on payment type, processor requirements, internal policy, and applicable NACHA rules. In general, businesses should retain ACH authorization records long enough to respond to disputes, return requests, and audits, and they should keep all supporting documentation together, including the final authorization, audit trail, and any verification notes.
Final thoughts
A fraudulent ACH authorization form is rarely just a document problem. It is a process problem, a verification problem, and often a training problem. Businesses that catch bad forms early usually do so because they have a repeatable review standard, not because they rely on instinct.
The best approach is practical and layered. Use clear standardized forms. Verify identity and authority. Review the form for consistency, not just completeness. Treat urgent and first-time requests as higher risk.
Confirm recurring setups carefully. Escalate questionable submissions instead of processing them by default. Keep thorough records so your team can defend legitimate debits and learn from disputed ones.
Most important, remember that ACH fraud prevention is not one rule or one tool. It is a disciplined habit built into intake, review, approval, and storage. Businesses that build that habit into their workflow are in a much better position to identify fake ACH authorization submissions, reduce unauthorized return risk, and protect cash flow before a bad debit ever gets processed.
Leave a Reply